Are you facing the nightmare of locked copyright assets? Refrain from letting your digital investment become inaccessible. A skilled copyright recovery specialist can navigate the complex problems and unlock your funds.
If you've fallen victim a hack, lost your private keys, or are impeded in a dispute, a copyright recovery expert has the expertise to assist you through the process.
They'll perform a thorough investigation to identify the root cause of your issue and formulate a tailored solution to regain your copyright assets.
Don't give up. Take measures now and contact a reputable copyright recovery expert who can assist you back to financial security.
Need to Breach Security?
Got a tight deadline and need those critical files quickly? Don't get stuck in the bureaucracy. We've got a team of elite hackers ready to penetrate your networks. Our experts can handle anything from phishing attacks to custom code injections. We work stealthily, so you can rest assured your hack will be undetectable.
- Contact us now
- Your success is our priority
Wallet Breached?! Get Your Assets Back with a Recovery Service
Having your copyright stolen is a nightmare. But don't lose hope! A skilled expert team can help you restore your lost coins. These dedicated professionals use advanced methods to trace the hackers and secure your funds.
Don't wait any longer to fight back. A trustworthy firm can give you the best opportunity of getting your copyright back.
ul
li Contact a reputable recovery specialist today.}
Need a Pro Hacker: Solutions for Data Retrieval & More
Data breaches and system compromises are becoming more common. If you've fallen victim to such an event, or simply need access to sensitive information, hiring a professional hacker might be your best option. Ethical hackers possess the skills to navigate security measures and retrieve lost data, regardless of its source. They can also pinpoint vulnerabilities in your systems, allowing you to bolster your defenses against future attacks. Remember that this should always be a last resort and conducted legally with full transparency.
- Retrieve lost data from compromised systems
- Expose security weaknesses in your infrastructure
- Execute penetration testing to simulate attacks and strengthen defenses
Reach out a reputable ethical hacking service today to discuss your specific concerns. They can provide a tailored solution to help you regain control over your data and protect your systems.
Secure Your Bitcoin Back
Have you suffered theft to a copyright scam? Don't give up hope. Our professionals of renowned copyright recovery agents are here to support you in recovering your lost Bitcoin. We know the pain of such a traumatic experience. With our unrivaled expertise, we strive to maximize your chances.
- Our services include:Securely analyzing the breach,Identifying potential avenues for recovery,Utilizing advanced blockchain forensic tools,Negotiating with malicious actors,Providing legal counsel and support
Contact us today for a free consultation. Let us help you reclaim your Bitcoin and restore your faith in the copyright world. Together, we can overcome this challenge.
Elite Hacking Services: Discreet and Effective Results
In the realm of cybersecurity, where data breaches and digital threats lurk around every corner, reliable hacking services have emerged as a critical line of defense. crypto recovery service Needing unparalleled expertise to analyze complex systems? Our team of seasoned ethical hackers possesses the knowledge and tools to deliver unobtrusive results that meet your specific needs. We specialize in executing comprehensive vulnerability assessments to identify weaknesses before malicious actors can exploit them. Privacy is paramount in our operations, ensuring that all engagements are handled with the utmost dedication.
- Enhance your defenses against cyberattacks.
- Expose vulnerabilities before they can be exploited.
- Gain invaluable insights into your infrastructure's security posture.
 Robert Downey Jr. Then & Now!
Robert Downey Jr. Then & Now! Marcus Jordan Then & Now!
Marcus Jordan Then & Now!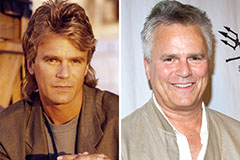 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now! Megyn Kelly Then & Now!
Megyn Kelly Then & Now! Ricky Schroder Then & Now!
Ricky Schroder Then & Now!